
This is the first in a series of security challenges.
These are designed to show ways of making Access apps reasonably secure.
The application is an ACCDE file so all VBA code has been removed.
The file has been renamed as a runtime file (ACCDR). It will not run if the file type is changed.
Startup properties have been modified.
There is no access to the navigation pane, ribbon or the rest of the application window
The taskbar has also been removed. It is restored automatically when the application closes
The application contains a number of 'deep hidden' tables (as well as the Access system tables)
These deep hidden tables cannot be viewed in the navigation pane.
The challenge is to:
a) find the name of each deep hidden table
b) determine the number of records in each table
c) find the contents of the memo/long text field for the third record in the table with the most records
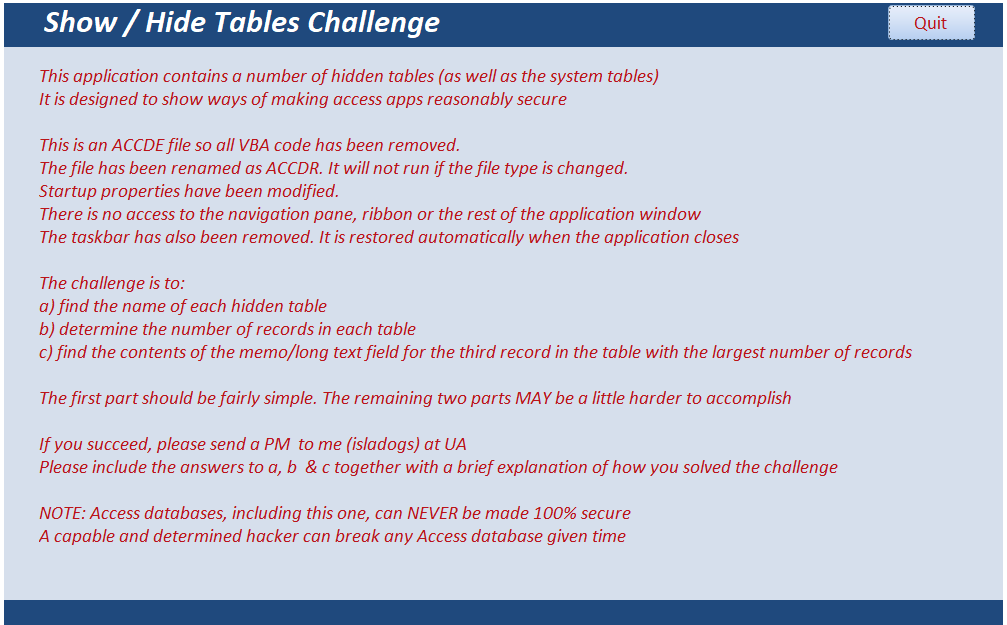
The challenge is intended to be solvable.
Once you have done the first part, the other two parts should (hopefully) be fairly simple.
To make things easier for this challenge, it has deliberately NOT been password protected.
I hope you enjoy puzzling out this challenge

If you succeed, please follow the supplied instructions to provide feedback by email (or use the feedback form provided below )
Please include the answers to a, b & c together with how you solved the challenge and the approximate time taken. Screenshots may be useful
NOTE: Access databases, including this one, can NEVER be made 100% secure
A capable and determined hacker can break any Access database given time

Download
Both 32-bit & 64-bit versions have been supplied
Click to download the correct version for your computer:
Show/Hide Challenge (32-bit) Approx 0.3 MB (zipped)
Show/Hide Challenge (64-bit) Approx 0.3 MB (zipped)

Feedback
Please use the contact form below to let me know whether you found this article interesting/useful or if you have any questions/comments.
Do let me know if you find any bugs in the application.
Please also consider making a donation towards the costs of maintaining this website. Thank you
Colin Riddington Mendip Data Systems Last Updated 30 Jun 2018

|
Return to Security Challenges Page
|
Return to Top
|
